Caesar Cipher
Encryption is a technique for protecting data confidentiality. Suppose Alice wants to send a message to Bob but does not want anybody else to be able to read the message. They can undertake the following steps to communicate securely:
Step 1: Alice and Bob choose an encryption method and a key.
Step 2: When Alice wants to send a message, she uses the encryption method, which takes the key and the message as input and outputs a ciphertext. The ciphertext usually reads like a meaningless text.
Step 3: Then Alice can send the message to Bob without worrying about it being read by others.
Step 4: When Bob receives the message, he decrypts the ciphertext using the key and obtains the original message.
Note that an encryption method usually comes with an associated decryption method. For simplicity, we will call an encryption/decryption method a cipher. In the above steps, the key for encryption and decryption are the same, so we call such methods symmetric ciphers.
Caesar cipher is perhaps the simplest and most widely known cipher. It is named after the Roman general and statesman Julius Caesar (100 BC - 44 BC), who used this method in his private correspondence. The key in Cassar cipher is simply a number between 0 and 25. The encryption method shifts the alphabet by a number of times indicated by the key so that each letter in the original message is mapped to a new letter in the ciphertext.
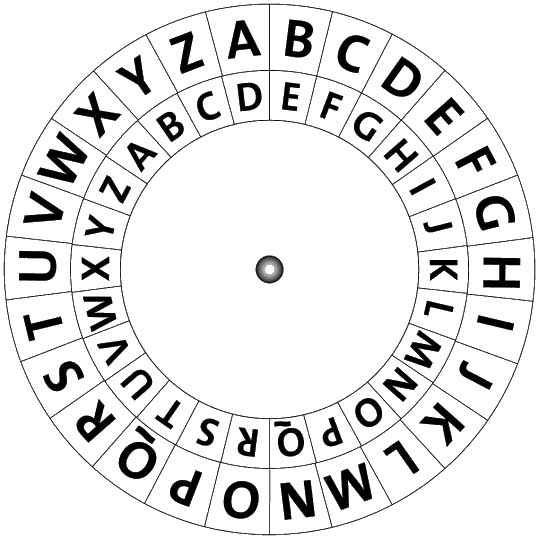
As an example, if the key is 3, we shift each letter in the English alphabet 3 positions to the right, as shown in the below figure, where the outer ring is the original alphabet, and the inner ring is the new alphabet. In this case, an A becomes a D, a B becomes an E, and so on. Note that we treat an alphabet as a circular list, so if we shift Z 3 positions to the right, we get C. Conversely, if we shift B 3 positions to the left, we get Y.
Suppose Alice wants to send the message "SEE YOU AT FIVE PM", the encrypted ciphertext is "VHH BRX DA ILYH SP". When Bob receives the ciphertext, he will map each letter back to the original alphabet, that is, an A becomes an X, a B becomes a Y, and so on. You can also understand it as shifting each letter 3 positions to the left. Then Bob should obtain the original message.
If the key is 0, then we shift each letter 0 times, which means we do not change the alphabet at all. In this case, the ciphertext is the same as the original message.