RSA Encryption
The first three weeks' ciphers use the same key for encryption and decryption; thus, those are called symmetric ciphers. Before establishing a secure communication channel, the parties need to share the secret key, and this can be tricky - if an attacker eavesdrops and steals the key, then the communication is no longer secure.
To protect against the above scenario, scientists have developed another type of ciphers - asymmetric ciphers. It is asymmetric because each party in the communication has two keys, one is used for encryption, and the other is used for decryption. More specifically, each party has a public key, which is used for encryption and can be shared with everyone, including adversarial attackers. Each party also has a private key (also called secret key), which is used for decryption and should not be shared with anybody. This kind of method is also called public-key encryption.
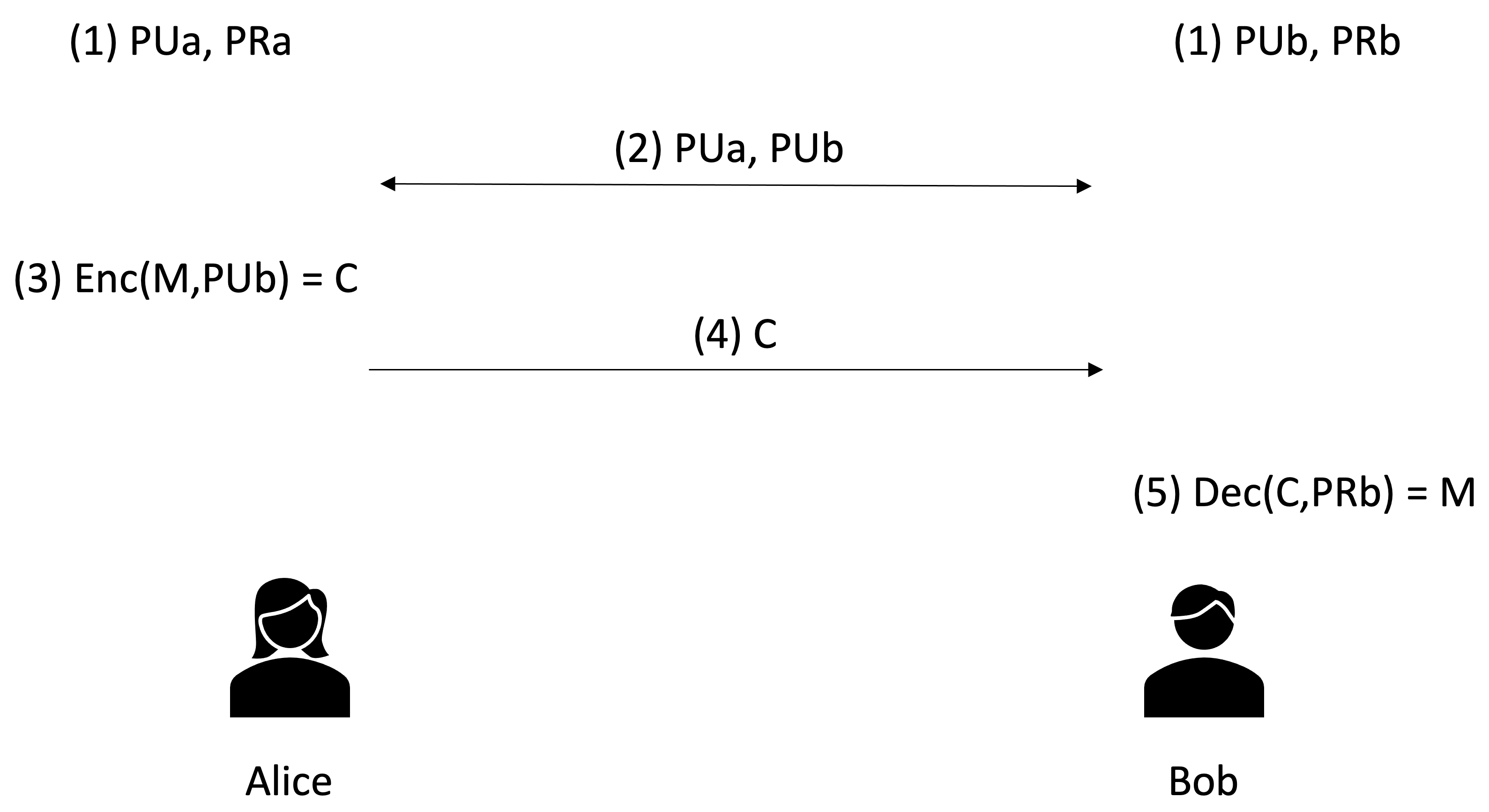
The general procedure of asymmetric encryption goes as follows: Assuming that Alice wants to send a message to Bob, (1) first, each of them needs to generate a public key and a private key. We name Alice's public key PUa; her private key is PRa. Bob's public key is PUb, and his private key is PRb. (2) Next, the communicating parties need to share their public keys. So Alice sends her public key PUa to Bob, and Bob sends his public key PUb to Alice. (3) When Alice wants to send a secret message (denoted by M) to Bob, she encrypts the message using Bob's public key PUb and obtains a ciphertext C. This process is denoted by Enc(M,Pub) = C. (4) Alice then sends the ciphertext C to Bob. (5) When Bob receives the ciphertext, he can decrypt it using his own private key PRb and obtain the original message M. This process is denoted by Dec(C,PRb) = M. The entire procedure is visualised in the figure below. Conversely, if Bob wants to send a message to Alice, he will encrypt the message using Alice's public key PUa and then the ciphertext across. Then Alice will decrypt the ciphertext using her private key PRa. We omit this part in the figure. In this method, even if an attacker intercepts all the communication and obtains the public keys and the ciphertext, without the private keys, it is impossible to decrypt the ciphertext.
But how come we can encrypt the message with a key and decrypt it with a different key? Well, now we need a little mathematics. There are numerous methods in this scheme; we will use the perhaps most famous one: the RSA public-key cipher. This method was developed by the mathematicians Ron Rivest, Adi Shamir and Leonard Adleman in 1977. (1) First, to generate the public key and the private key, we will need to choose two prime numbers, p and q. Recap: a prime number is a natural number that is greater than 1 and is not a product of any two smaller numbers. Let n = p * q. (2) By convention, we define phi(n) = (p-1)*(q-1). Then we need to choose another prime number e such that 1 < e < phi(n). (3) Next, we find a number d such that (e * d) mod phi(n) = 1 mod phi(n). Here, mod stands for the modulo operator. That is, x mod y returns the remainder of x / y. Once we have found p, q, e and d, we can generate the public key as the pair of (n,e), and the private key as (n,d).
To encrypt a message M, which we assume is a number, we simply compute the following: Enc(M,(n,e)) = M^e mod n = C, where M^e means M raised to the power of e. To decrypt a ciphertext C, we compute the following: Dec(C,(n,d)) = C^d mod n = M.
For example, let us pick p = 3 and q = 11. Then n = p * q = 33. We then choose e = 3, and find d = 7. You can check that (e * d) mod phi(n) = 1 mod phi(n), that is, 21 mod 20 = 1 mod 20. Therefore, the public key is (33,3), and the private key is (33,7). Say the message M is the number 4. The encryption goes Enc(4,(33,3)) = 4^3 mod 33 = 31. So 31 is our ciphertext. To decrypt 31, we compute Dec(31,(33,7)) = 31^7 mod 33 = 4, and we obtain the original message!